Interested in becoming your own web security expert? Now you can! Cloudbric first introduced Cloudbric Labs last November as a collection of free security tools for the cybersecurity community.
This is why the resources are available to anyone and everyone, easy to utilize, and free of charge. Currently, Cloudbric Labs consists of three distinct services and tools: BlackIPedia, Threat Index, and WAFER.
In this blog post, we will show you how to get the most out of these free security tools.
 BlackIPedia
BlackIPedia
What Is It?
In a nutshell, BlackIPedia is an IP reputation service that allows users to check IP threat levels, with the term “black” being synonymous with “malicious.” Cloudbric Labs assigns a numerical value (or threat level) — on a scale from 1 to 100 — to an IP address based on the type and range of web attacks originating from it and frequency. The lower the number, the less of a threat it poses. For reference, an IP address with a threat of 70 or higher would be considered malicious.
Who’s It For?
As previously mentioned, the service is available to everyone, including users who are not currently protected by Cloudbric’s website security services. BlackIPedia is designed to be useful to website owners and developers who want to prevent cyberattacks. Cloudbric Labs provides BlackIPedia API documentation so that the data can be integrated into end-users’ own security platforms, and thus allow website owners to take preemptive action in blocking malicious IPs from accessing their site.
How Do You Use It?
Simply input a valid IP address in the search bar to generate a security report that details web attack history, current threat level, country of origin, and more. Take a look at a report sample below (click to enlarge). Users can also look at the top 100 blacklisted IPs by date.
Users can also look at the top 100 blacklisted IPs by date.
 Threat Index
Threat Index
What Is It?
Cloudbric Labs’ Threat Index is a database of web vulnerabilities, consisting of a comprehensive list of unique vulnerability strains that are associated with some of the web’s most common attacks like SQL injection.
Who’s It For?
The Threat Indexis available for reference to people that are interested in reviewing the different kinds of threats on the web. From cybersecurity fans to Cloudbric users, anyone interested to find out what type of web vulnerabilities have been detected and blocked by Cloudbric’s WAF can do so via the Threat Index. The Cloudbric Labs’ team rates each web vulnerability from Low to Critical, depending on their potential impact for damage on major platforms.
How Do You Use It?
You can browse through analyzed reports of the most recent vulnerabilities by searching a keyword or phrase, like XSS and SQL Injection, or a simple description of the threat’s general characteristics in the search bar. Alternatively, you can also view a general list of the recent web vulnerabilities by the date they were updated with new information. This is different from the published date, which derives from the date it was crawled by our team in its original source. See an example of a web vulnerability report below!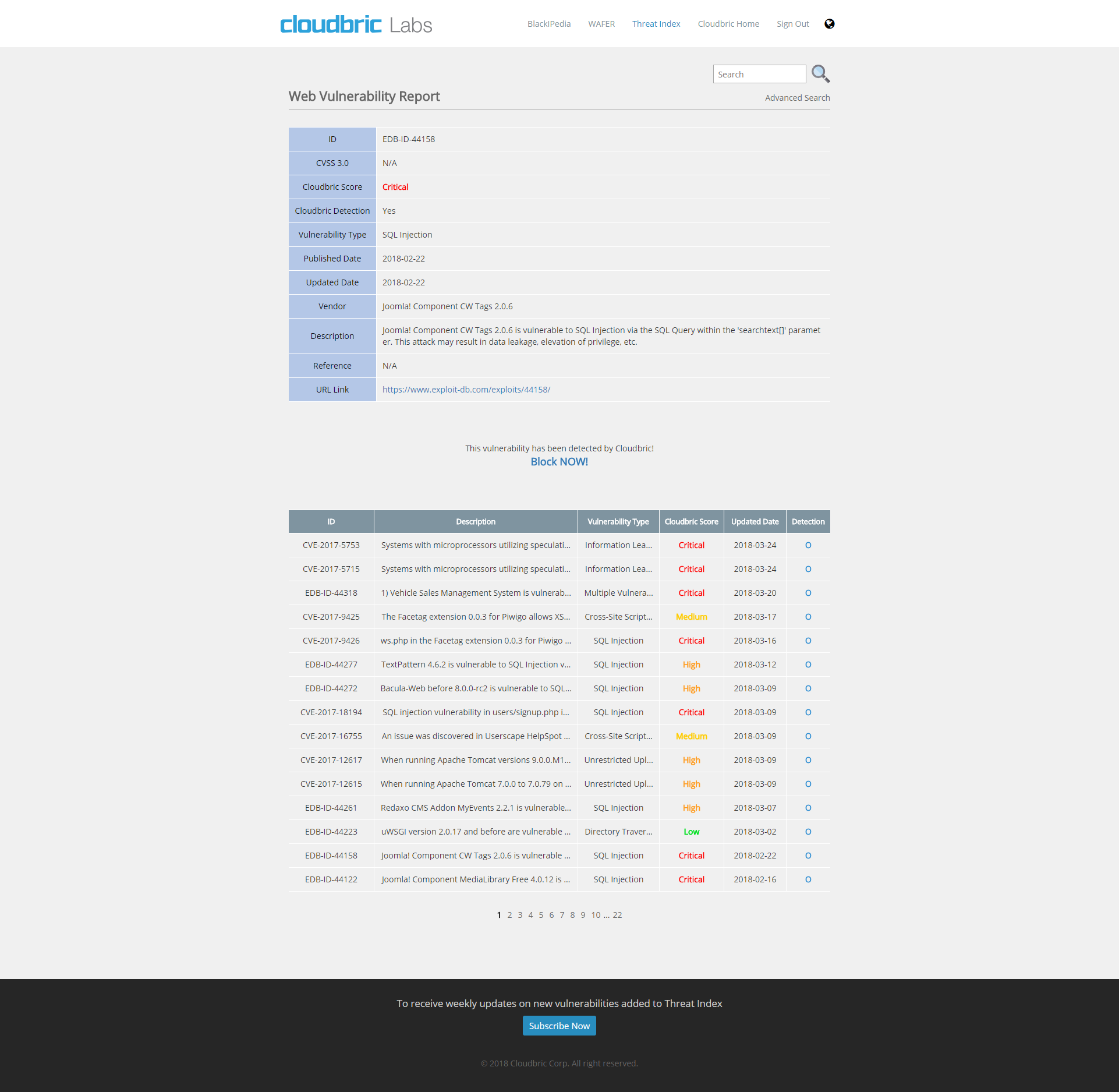
 WAFER
WAFER
What Is It?
WAFER is a WAF evaluator that tests the performance and detection abilities of the most popular WAFs in the market by focusing primarily on the percentage of false positives and false negatives. When it comes to testing the accuracy of security services like cloud-based WAFs, calculating false positives and false negatives are an objective method to measure a WAF’s detection capabilities.
Who’s It For?
Not all WAFs are created equal, and difference in performance and accuracy is to be expected. WAFER is recommended for website owners, administrators, and developers who seek to optimize their web security (or that of their customers) by testing out different WAFs to find the one best suited for their security needs and budget. Anyone can utilize WAFER to check whether their current WAF is doing an adequate job of protecting their websites.
How Do You Use It?
To test the performance of a WAF, website owners are asked to enter their domain and choose the WAF they are currently using or interested in testing. Akamai, Cloudflare, F5, Sucuri, Wordfence, and Fortinet are just some of the WAF options. Users are then asked to verify ownership of the domain by (1) simply signing into their Cloudbric account, (2) changing their domain’s DNS record, or (3) by adding a meta tag to their HTML code on their website. WAFER evaluates performance by sending a test traffic to the site; Cloudbric Labs uses Exploit DB* and attack patterns to conduct this test, and upon test completion, a downloadable evaluation report is provided. In this summary report, a letter grade from A to D is assigned (A noting the highest accuracy) to both the WAF’s detection and distinguishing abilities. See an example of the evaluation report below.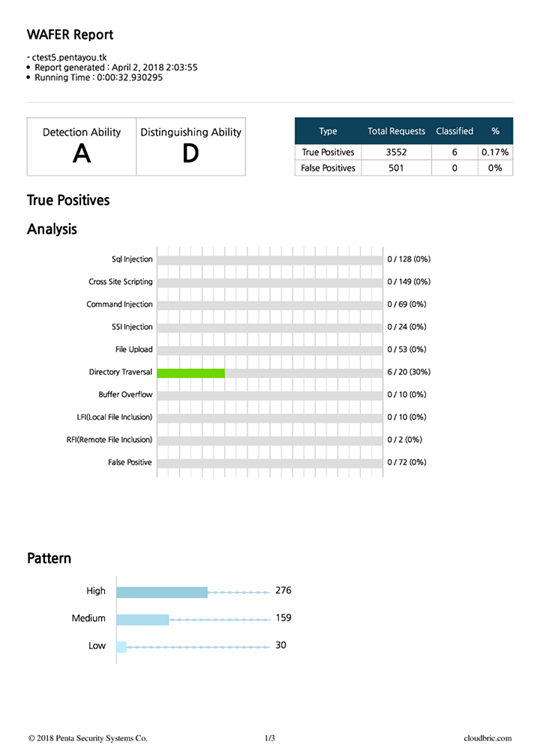
Even if you do not currently own a website, we have other resources available for you to reference, like a case study that highlights the performance test results of Cloudbric’s WAF in comparison to another vendor’s WAF. Click here to read the full report.
Head over to labs.cloudbric.com now to get access to the free security tools!
Notes:
*Exploit DB* patterns are obtained from a comprehensive database of exploit codes maintained by Offensive Security, a respected and well-established information security training company. They also provide various information security certifications as well as premium penetration testing services.





