Enterprise Security Rules for Secure Workation
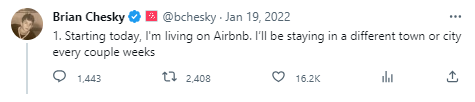
 On January 2022, Brian Chesky, the CEO of Airbnb, tweeted his remote work plan on his account. Four months later, Airbnb expanded its work-from-anywhere policy for every employee.With the rise of remote work since the pandemic, a new working trend known as “workation” (also known as workcation; a compound word of work and vacation) has emerged, leading to many countries around the world actively issuing work visas.Similarly, Korea has announced plans to introduce a digital nomad visa (work visa) for foreigners seeking extended stays during the second half of this year, allowing them to remain for up to two years.Workation is rapidly emerging as the trendiest form of work these days. But is it safe to adopt?
On January 2022, Brian Chesky, the CEO of Airbnb, tweeted his remote work plan on his account. Four months later, Airbnb expanded its work-from-anywhere policy for every employee.With the rise of remote work since the pandemic, a new working trend known as “workation” (also known as workcation; a compound word of work and vacation) has emerged, leading to many countries around the world actively issuing work visas.Similarly, Korea has announced plans to introduce a digital nomad visa (work visa) for foreigners seeking extended stays during the second half of this year, allowing them to remain for up to two years.Workation is rapidly emerging as the trendiest form of work these days. But is it safe to adopt?
Vulnerabilities in the Remote Work Environment
 Recently, an increasing number of companies are adopting workation systems to enhance employee morale and productivity. However, with employees working from various locations outside designated offices, strengthening computer security becomes a challenge, leading to a higher risk of exposure to cyber threats such as hacking.Remote work opens the door to potential data leaks and losses when using unsecured public Wi-Fi or accessing internal networks with personal devices that may be vulnerable to malware (e.g., PCs, tablets, smartphones). These security vulnerabilities pose significant risks to the company.In this relatively vulnerable remote work environment, hackers may target the enterprise’s internal systems, attempting to breach and compromise sensitive information.
Recently, an increasing number of companies are adopting workation systems to enhance employee morale and productivity. However, with employees working from various locations outside designated offices, strengthening computer security becomes a challenge, leading to a higher risk of exposure to cyber threats such as hacking.Remote work opens the door to potential data leaks and losses when using unsecured public Wi-Fi or accessing internal networks with personal devices that may be vulnerable to malware (e.g., PCs, tablets, smartphones). These security vulnerabilities pose significant risks to the company.In this relatively vulnerable remote work environment, hackers may target the enterprise’s internal systems, attempting to breach and compromise sensitive information.
Essential Security Systems for Corporations
 From a web security perspective, the expansion of remote work environments introduces a significant challenge as numerous external devices gain access to the enterprise network, consequently increasing the risk of potential threats.Various cyber threats emerge when remote workers access corporate systems through public network environments, and create and share sensitive data in cloud services. As a response to these challenges, the concept of Zero Trust emerged as an alternative security approach.Zero Trust is a security concept designed to continuously validate users and devices to safeguard corporate resources, adhering to the principle of “Never Trust, Always Verify.” By consistently requiring user verification, even after access has been granted, this approach ensures more robust protection for corporate data.
From a web security perspective, the expansion of remote work environments introduces a significant challenge as numerous external devices gain access to the enterprise network, consequently increasing the risk of potential threats.Various cyber threats emerge when remote workers access corporate systems through public network environments, and create and share sensitive data in cloud services. As a response to these challenges, the concept of Zero Trust emerged as an alternative security approach.Zero Trust is a security concept designed to continuously validate users and devices to safeguard corporate resources, adhering to the principle of “Never Trust, Always Verify.” By consistently requiring user verification, even after access has been granted, this approach ensures more robust protection for corporate data.
📌 Core Principles of Zero Trust for Enterprise Security
The authentication system needs to be fortified for users and devices accessing corporate systems in remote working environments outside the office. To enhance security, companies can adopt multiple authentication methods, including email-based authentication codes, One Time Password (OTP), alongside the conventional ID and password-based authentication we commonly use.
However, passing the validation does not guarantee 100% reliability. Therefore, implementing segmented access management becomes crucial. By granting users minimal access, limited to the resources they genuinely require based on their rank and permissions, data can be safeguarded, and the risk of data leakage is significantly reduced, effectively preventing user misuse.
—
Cloudbric offers Cloudbric PAS (Private Access Solution) to address enterprise security concerns in the evolving hybrid work environment, where internal and external boundaries are gradually disappearing due to workation, telecommuting, and remote work.
📌 Learn more about Cloudbric PAS
Secure your in-house systems against potential security threats with Cloudbric PAS (Private Access Solution), a zero-trust network access (ZTNA) security solution offering multiple authentication methods and segmented access management.





