Today, we will continue our discussion based on the Types of Attacks – DDoS Part 1. This will be a more in-depth look at how DDoS attacks are carried out. Let’s get started!
Ping Flood Attacks
This is a type of DDoS attack where an attacker focuses on ping flooding the ICMP packets of a victim’s network. This is more successful carried out if the attacker’s bandwidth is greater than the victims. Here are some more tidbits of ping flood attacks:
- Aim of this attack is to overwhelm the capacity of the network connection to the target organization
- Traffic can be handled by higher capacity links on the path, but packets are discarded as capacity decreases
- Source of the attack is clearly identified unless a spoofed address is used
- Network performance is noticeably affected
UDP Flood
This type of denial of service attack relies on attacking the User Datagram Protocol (UDP) of a victim’s network. It essentially send a high number of UDP packets to random ports to a remote or victim host. Most attackers in this type of attack also try to use IP spoofing to really cover their tracks and to keep their identities a secret.
TCP SYN Flood

TCP SYN flood attacks are attacks on systems connected to the internet and provides TCP network services (i.e. web server, FTP server, or mail servers). TCP SYN floods occur when an attacker sends SYN requests to a target’s system to essentially use up all of a server’s resources.
To better understand this, usually a TCP requires a “three-way handshake”, which is a reference to how TCP connections work. They are the basis for this form of attack. The SYN-ACK communication process works like this:
- First, a “synchronize”, or SYN message, is sent to the host machine to start the conversation
- Next, the request is “acknowledged” by the server. It sends an ACK flag to the machine that started the “handshake” process and awaits for the connection to be closed
- The connection is completed when the requesting machine closes the connection
A SYN flood attack will send repeated spoofed requests from a variety of sources at a target server.
- Sends TCP packets to the target system.
- Total volume of packets is the aim of the attack rather than the system code.
As one can see, DDoS attacks are not only wide ranging, but also highly complicated. To make matters worse, attackers can fully take advantage of IP spoofing that makes their identities virtually untraceable.
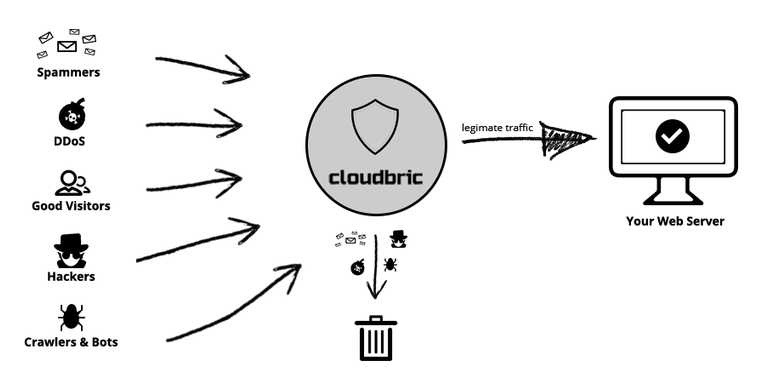
Keep yourself protected against these attacks by signing up for Cloudbric today! We protect against all DDoS attacks for free (typically a $200+ feature on many competitor sites)!





