When the best online security practices are being discussed, there’s always someone that brings up either two-factor authentication (2FA) and multi-factor authentication (MFA). This is because more and more online services are recognizing the need to ensure a higher level of security for online accounts.
Two-factor authentication and multi-factor authentication add additional levels of user verification during the login process, making it a bit more difficult for hackers to gain access to these accounts.
This blog post will discuss their differences as well as dispel confusion about the processes, especially when two-step authentication or three-step authentication is thrown into the mix.
Authentication Factors
In order to understand the differences between two-factor and multi-factor authentication, you need to first understand the concept behind an authentication factor. Loosely defined, an authentication factor is a category of methods for verifying a user’s identity when requesting access to a system. Simply put, it makes sure that they are who they say they are. Each category is considered a factor. But because usernames and passwords fall are under the same factor, when combined they form what is known as single-factor authentication (SFA). Overall, authentication factors can be divided into generally three categories: knowledge, possession, and inherence factors. It’s important to note that there are more than just these categories but generally most online accounts utilize these three.
- A knowledge authentication factor includes information only a user should know (i.e username, password)
- A possession authentication factor includes credentials retrieved from a user’s physical possession, usually in the from a hardware device (i.e. security token, software token mobile phone used)
- An inherence authentication factor includes a user’s identifiable biometric characteristic (i.e. fingerprint, voice, iris scan)
Single-Factor vs Two-Factor vs Multi-factor Authentication
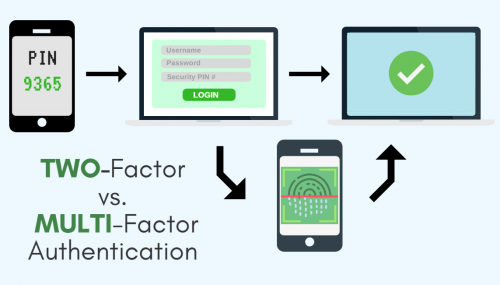
Based on the categories described, single-factor authentication requires credentials from only one of these categories. Meanwhile, two-factor authentication involves two of the categories, and finally multi-factor authentication requires credentials from at least two or more categories. Two-factor authentication should not be confused with two-step verification (2SV). Usually, when users sign up for an online service and are asked to create an account for the first time, they are prompted to create a standard username and password. They are thereafter asked to verify their identity through a one-time code which is delivered via either an email, text message or phone call. While at first glance seeming to be the same, since a device may be involved, two-step verification differs from two-factor authentication. In a two-step verification process utilizing such one-time codes, only the knowledge authentication factor is involved, rather than two different factors. This is because the device itself is not key to successful authentication – the code is, which can be intercepted without possessing the device. Two-step verification should therefore not be used interchangeably with two-factor authentication.
Who Uses Two-Factor Authentication and Multi-Factor Authentication?
These days, choosing strong passwords may not be enough to keep hackers away. Two-factor authentication adds an extra layer of protection to keep online accounts safe. While many popular online services (e.g Gmail, Yahoo, LinkedIn, Instagram) are utilizing single-factor authentication, not all are implementing it just yet. Even rarer is the number of organizations using multi-factor authentication with more than just two factors. But for the financial, health, and government sectors multi-factor authentication is a must, especially when data is an organization’s greatest asset. In most cases it is in these sectors that customers expect the highest level of security to be implemented. Two-factor authentication and multi-factor authentication add an extra layer of security on all your online accounts. However, enabling these additional steps doesn’t mean you should ignore common security practices like creating strong passwords or changing them regularly. Read on for more online safety tips here!





