- Security Platform

WAAP
An Advanced Web Firewall, Effectively Counters Web Attacks, Bot Attacks, DDoS Attacks, and API Attacks
ZTNA
Robust Authentication Security Solutions Covering User Authentication to IoT Devices
CTI
Big Data Based Cyber Threat Information Sharing Platform
Public Cloud Security
Simplified Solution for the Complex Security Policies of Convenient Cloud Services
Security Apps
Ensuring Secure Personal Internet Access and Preventing Phishing and Smishing Damage with a Single Click - Solutions

By Use Cases
Applications of Cloud Security Platform - Resources
- Partners
- Support
- Company
WAAP
Public Cloud Security
ZTNA
Security Apps
CTI

Cloudbric WMS
Simplified Management for Complex AWS WAF Dedicated Dashboard for Quick Overview
An intuitive user interface enables effortless monitoring and management of AWS WAF’s security status for both experts and non-experts.

Cloudbric WMS
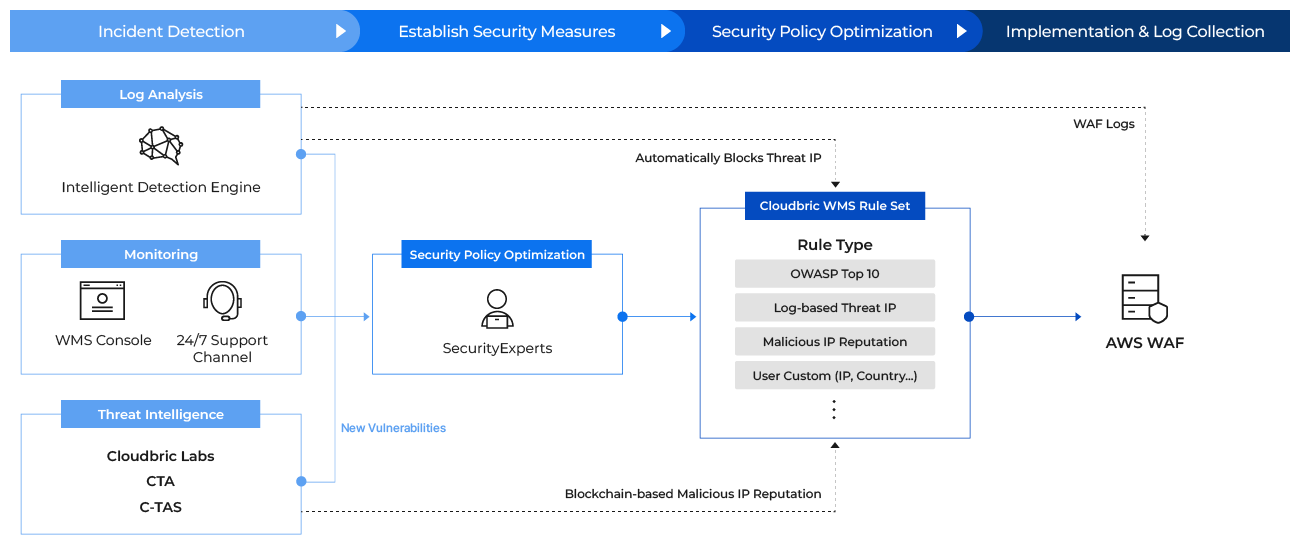
Intelligence-based Security Policy Operation and Management Service
Cloudbric WMS(WAF Managed Service) provides systematic security policy management services such as configuring and monitoring the Rule Set for the customer environment to optimize the Cloud Service Provider Web Application Firewall (CSP WAF).
Cloudbric WMS
Why is Managed Service necessary?
Operating and managing Web Application Firewalls (WAF) provided by Cloud Service Providers (CSPs) like Amazon Web Services (AWS) or Microsoft Azure can be extremely challenging for those without expertise. Easily Manage AWS WAF, Even Without Dedicated Personnel or Security Expertise with Cloudbric WMS.
Secure and Convenient Management
· Optimized Security Policies by Experts
· Automatic Log Analysis System
· Automatic Log Analysis System
Enhanced Service Reliability
· Rule Set with High Detection Rates
· Systematic Risk Detection and Response
· Resolve Fundamental Causes Through Log-Based Response
Cost Saving in Operations
· Reduced Human Resources for Security Policy Operation
· Minimized Unnecessary Costs Through the Hacking Prevention
· Minimized Unnecessary Costs Through the Hacking Prevention
Enhanced Corporate Image
· Smooth Operations via Cybersecurity Preparedness
· Increased Customer Trust via Secure User Information Management
· Increased Customer Trust via Secure User Information Management

Dedicated Dashboard
for Monitoring
Cloudbric WMS provides a dedicated dashboard with an intuitive UI for security status management of the website. The user console within the dashboard provides web ACL log analysis data covering the previous three months, facilitating evaluation of cyber threat statuses and simplifying rule configuration and override.
Globally Recognized Technology
Leverage the expertise of industry-leading security professionals with over 27 years of experience to optimize security policies. Swiftly counter advanced cyber attacks using Threat DB recognized by the Cyber Threat Alliance (CTA), an alliance of the world’s foremost security corporations.

Cloudbric WMS
Service Offering
Security Policy
Consulting
Consulting

Customized Consulting based on User Logs
Security policy for OWASP Top 10 Response
Provide Malicious IP Reputation
Security Policy
Operations
Operations
Intelligence-based Optimization System
Dual Security via Automated Threat IP Blocking
New Vulnerabilities Response

Operating an Up-to-date Threat Information Analysis System
Early Detection and Response to New Vulnerabilities
User Console

Visualized Threat Information Interface
Setting Automation for User Convenience
(Includes approx. 3 months of log management)
(Includes approx. 3 months of log management)
Security Reports

Automated Real-time Log Analysis
Provide Threat Insight
(Available in PDF format)
(Available in PDF format)
Customer Support

24/7 Support Channel
Tech Support in KR/EN/JP with False-positive Response
Cloudbric WMS
Fast and Convenient Implementation Without Installation
Cloudbric WMS offers a robust managed service without the need for installation or DNS settings.
